With a ring or a ping, scammers come calling and texting.
It probably happens often enough. You get a call from an unknown number, and you wonder if you should even bother answering it. It’s probably a scammer. Or is it? What if it’s something important? You answer. Sure enough, it’s a robocall. But the voice says it’s your bank and that there’s a problem with your account. Now what do you do?
Same things with texts. Maybe you get a message that goes something like:
“We have detected unusual activity on your account. Please call this number to speak to a customer service representative.”
Enter the world of vishing and smishing.
The term vishing stems from a combination of “voice” and “phishing.” Likewise, smishing comes from a combination of “SMS” (text) and “phishing.” Taken all together, they’re two ways that scammers will try and reach you on your phone.
The con is the same as it always is with any form of phishing. The scammers want things like credit card numbers, account logins, and other personal information so that they can rip you off or steal your identity altogether.
Yet you have ways you can protect yourself. And you have tools that might help you reduce the number of scam calls and texts you get in the first place.
How do vishers and smishers get your phone number?
The scammers behind these attacks often cast a wide net. They send calls and messages to thousands and thousands of phones in one fell swoop. Even if they catch a tiny percentage of victims, the attack can still return a decent profit.
The secret is volume, and scammers can get phone numbers in bulk in several ways:
- Data breaches: While some data breaches involve the loss of credit card and government ID numbers, others involve names, email addresses, and phone numbers. That’s still damaging, because these breaches provide hackers and scammers with the basic information they need to launch all kinds of phishing, vishing, and smishing attacks.
- Data brokers: Scammers can also buy entire lists of numbers for a few dollars with a few clicks. Online data brokers collect and sell highly detailed information about millions of people. The records vary from broker to broker, yet they can include dozens or even hundreds of entries gathered from public sources and from third parties. Data brokers will often sell such lists to advertisers for targeted campaigns—but they’ll sell them to scammers too. Data brokers will sell to anyone.
- The dark web: Plenty of personal information ends up in dark web marketplaces. Scammers will often share lists of potential victims with other scammers for free. In other cases, they’ll sell them for a profit. Either way, the dark web provides scammers with several resources for obtaining phone numbers.
- Dumpster Diving: And old-school “hack” involves digging through a bank or business’ dumpster and salvaging any lists of client phone numbers. With that list, scammers can program the numbers into their dialers for a more targeted attack.
- Auto-dialers: As the name suggests, this piece of gear calls random phone numbers with a recorded message. Sometimes, scammers will make calls to specific area codes with a message that involves a regional bank or credit union. This way, the scammer takes aim at potential members in the targeted area.
What are some examples of smishing?
There’s a good chance you’ve seen several examples of smishing yourself. Maybe you’ve come across something like these:
- “Hi! We noticed that you’re a recent customer of ours. To finish setting up your account, please tap this link and enter your personal information.”
- “Urgent! Your bank account has been compromised. Please tap this link to reset your password and prevent any further fraud.”
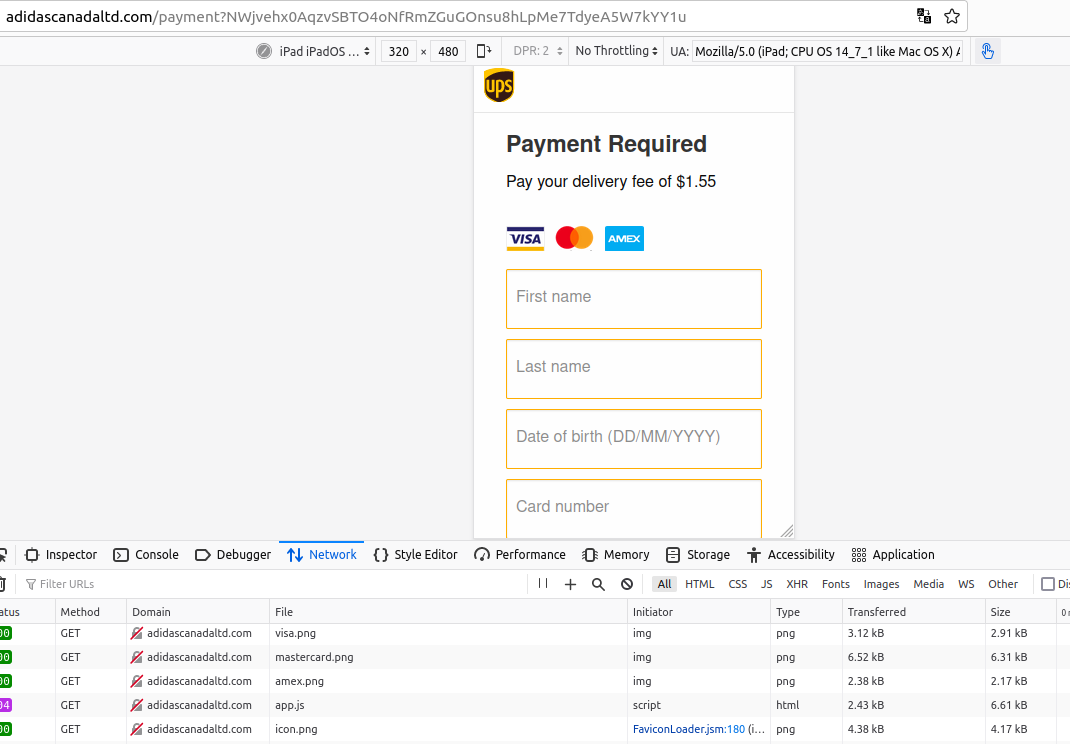
- “We have a package for you, but we were unable to deliver it. Please tap this link to update your information so that we can get your package to you.”
- “Hi! It’s me, Mandy. Are we still on for lunch today?”
- “You owe back taxes. Pay using this link within three days or we will turn your case over to law enforcement.”
Messages like these can seem plausible at first, until you look at them more closely.
First off, they usually include a link. The link might include unusual strings of characters and a web address that doesn’t match who the message says it’s coming from. Like a bogus notice from the post office that doesn’t use the official post office URL. Or, the link might look almost like a legitimate address, but changes the name in a way that indicates it’s bogus.
Another indicator might be that you don’t know “Mandy” at all. This is by design. In fact, the scammer hopes you don’t recognize the name. They want you to respond with a “sorry, wrong number” text. From there, the scammer will try to strike up a conversation and launch the first steps of a romance scam or a similar con game.
Lastly, the message might employ a scare tactic or threat. Scammers love this approach because it successfully plays on people’s emotions and gets them to act quickly without much thinking. The bank and tax scares offer a couple prime examples of this approach. As do messages that appear to come from family members who say they’re in trouble. Like their car has broken down in the middle of nowhere or that they’re off to urgent care with a sudden illness.
In all, the scammers behind these texts are after the same thing—your personal information, money, or a combination of both.
How to protect yourself from vishing and smishing attacks
- Don’t trust caller ID: Scammers can tamper with caller ID. Scammers have several tools available that can help them populate the caller ID with a specific bank or credit union, or with the words “Bank” or “Credit Union.”
- Follow up directly: If you receive a phone call from a person or a recording requesting personal information, hang up. If the call appears like it came from a trusted organization, call them directly to confirm their request. Do the same for any texts that ask you to select a link to provide information.
- Report any fraud attempts immediately: Document the call, note what was said, what was asked for, and the number the caller or texter used. Report this to the company in question. Many organizations have dedicated fraud pages that have email addresses to report fraud committed in their name. Netflix offers a good example, and so does the Internal Revenue Service (IRS) in the U.S. McAfee has a page dedicated to fraud as well.
- Look for errors in spelling or grammar. Legitimate businesses and organizations go to great lengths to ensure their messages are free from mistakes. Scammers, less so. Misspellings and awkward sentences often find their way into smishing attacks.
- Contact the sender: Did you get an urgent text message from someone who appears to be a friend or family member? Follow up with them in some way other than responding to the text message you just received, particularly if it came from a new or unknown number.
- Don’t tap on links in text messages: If you follow one piece of advice, it’s this. As mentioned above, if you have concerns, follow up directly.
Another way to cut down on scam calls and texts: online protection software
With comprehensive online protection software like McAfee+ on your smartphone, you can stay safer in several ways.
It offers web protection that warns you of sketchy links in texts, search, and while you browse, which can steer you clear of websites that steal information. It can also monitor dozens of pieces of personal information and alert you if any of it appears on the dark web—and offer guidance for what to do next.
Further, it can help you remove your personal information from data broker sites with our Personal Data Cleanup. You’ve seen how scammers use data brokers to create their call and text lists. Telemarketers turn to data brokers for the same reason too. Removing your information can lower your exposure to data brokers and telemarketers alike and help reduce scam and spam calls as a result.
When it comes to vishing and smishing, you have several tips, tactics, and tools at your disposal. When in place, they can help prevent scammers from ringing and pinging—or fooling you if they still somehow do.
The post Those Annoying Scam Calls and Texts: How to Fight Back Against Vishing and Smishing appeared first on McAfee Blog.
—————
Free Secure Email – Transcom Sigma
Boost Inflight Internet
Transcom Hosting
Transcom Premium Domains