The Russian government has for the past four years been fighting to keep 29-year-old alleged cybercriminal Alexei Burkov from being extradited by Israel to the United States. When Israeli authorities turned down requests to send him back to Russia — supposedly to face separate hacking charges there — the Russians then imprisoned an Israeli woman for seven years on trumped-up drug charges in a bid to trade prisoners. That effort failed as well, and Burkov had his first appearance in a U.S. court last week. What follows are some clues that might explain why the Russians are so eager to reclaim this young man.

Alexei Burkov, seated second from right, attends a hearing in Jerusalem in 2015. Andrei Shirokov / Tass via Getty Images.
On the surface, the charges the U.S. government has leveled against Burkov may seem fairly unremarkable: Prosecutors say he ran a credit card fraud forum called CardPlanet that sold more than 150,000 stolen cards.
However, a deep dive into the various pseudonyms allegedly used by Burkov suggests this individual may be one of the most connected and skilled malicious hackers ever apprehended by U.S. authorities, and that the Russian government is probably concerned that he simply knows too much.
Burkov calls himself a specialist in information security and denies having committed the crimes for which he’s been charged. But according to denizens of several Russian-language cybercrime forums that have been following his case in the Israeli news media, Burkov was by all accounts an elite cybercrook who primarily operated under the hacker alias “K0pa.”
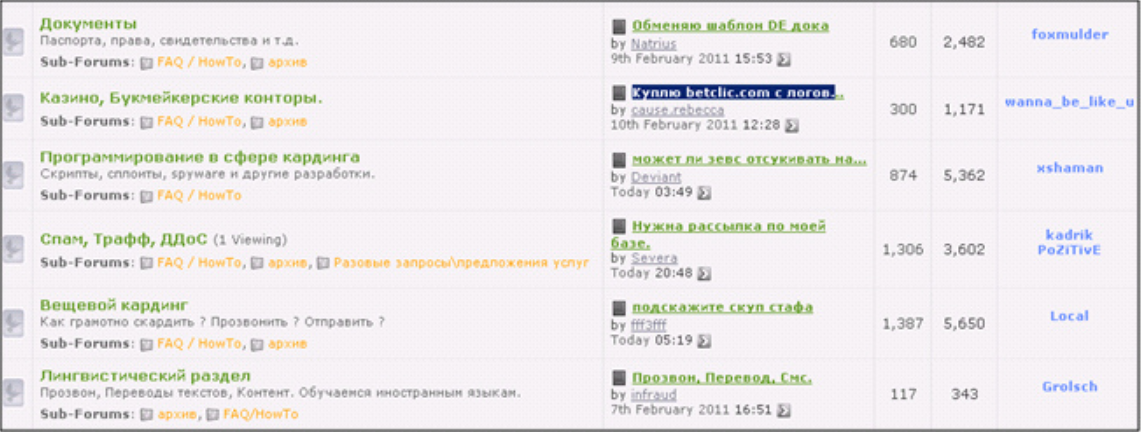
This is the same nickname used by an individual who served as co-administrator of perhaps the most exclusive Russian-language hacking forums ever created, including Mazafaka and DirectConnection.
Since their inception in the mid-aughts, both of these forums have been among the most difficult to join — admitting only native Russian speakers and requiring each applicant to furnish a non-refundable cash deposit and “vouches” or guarantees from at least three existing members. Also, neither forum was accessible or even visible to anyone without a special encryption certificate supplied by forum administrators that allowed the sites to load properly in a Web browser.
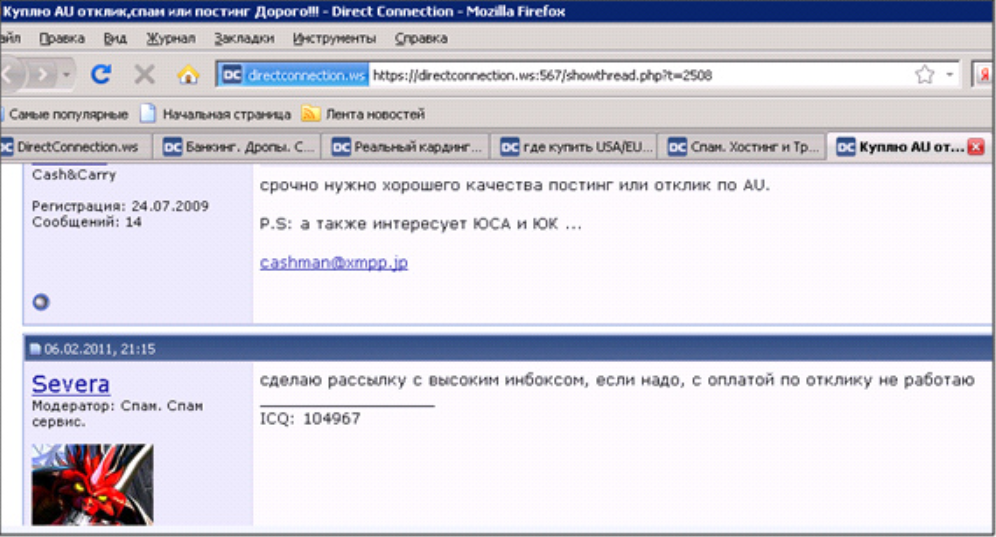
DirectConnection, circa 2011. The identity shown at the bottom of this screenshot — Severa — belonged to Peter Levashov, a prolific spammer who pleaded guilty in the United States last year to operating the Kelihos spam botnet.
Notably, some of the world’s most-wanted cybercriminals were members of these two highly exclusive forums, and many of those individuals have already been arrested, extradited and tried for various cybercrime charges in the United States over the years. Those include convicted credit card fraudsters Vladislav “Badb” Horohorin and Sergey “zo0mer” Kozerev, as well as the infamous spammer and botnet master Peter “Severa” Levashov.
A user database obtained by KrebsOnSecurity several years back indicates K0pa relied on the same email address he used to register at Mazafaka and DirectConnection to register the user account “Botnet” on Spamdot, which for years was the closely-guarded stomping ground of the world’s most prolific spammers and virus writers, as well as hackers who created services catering to both professions.
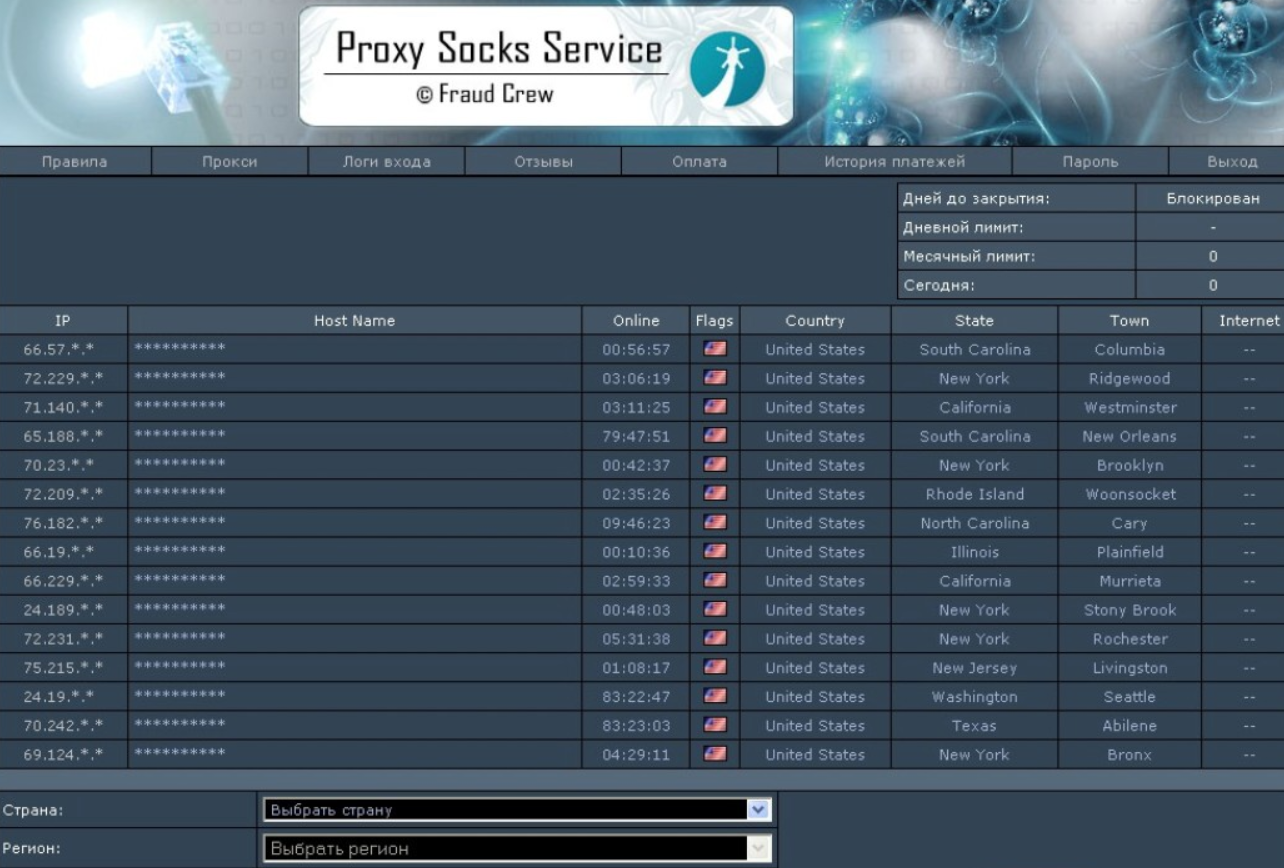
As a reporter for The Washington Post in 2008, I wrote about the core offering that K0pa/Botnet advertised on Spamdot and other exclusive forums: A botnet-based anonymity service called FraudCrew. This service sold access to hacked computers, which FraudCrew customers used for the purposes of hiding their real location online while conducting cybercriminal activities.
K0pa also was a top staff member at Verified, among the oldest and most venerated of Russian language cybercrime forums. Specifically, K0pa’s role at Verified was in maintaining its blacklist, a dispute resolution process designed to weed out “dishonest” cybercriminals who seek only to rip off less experienced crooks. From this vantage point, K0pa would have held considerable sway on the forum, and almost certainly played a key role in vetting new applicants to the site.
Prior to his ascendance at these forums, K0pa was perhaps best known for being a founding member of a hacker group calling themselves the CyberLords. Over nearly a decade, the CyberLords team would release dozens of hacking tools and exploits targeting previously unknown security vulnerabilities in Web-based services and computer software.
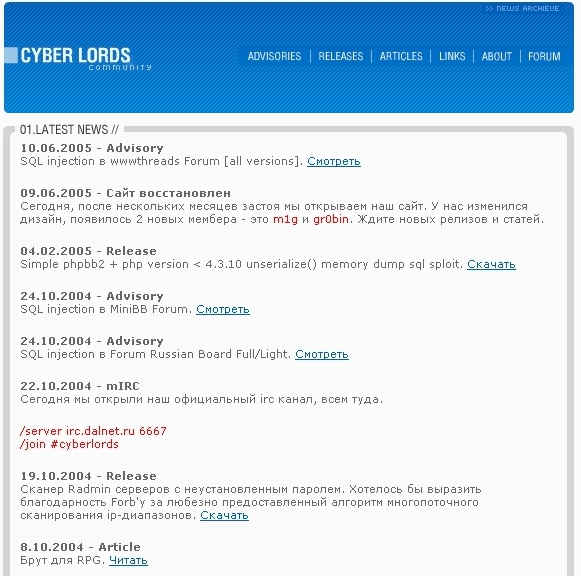
A cached copy of cyberlords[.]ru, circa 2005.
A DIRECT CONNECTION?
According to security firm Cybereason, Russia has a history of using contractors — even cybercriminals — to run intelligence operations. These crooks-turned-spies “offer a resource to the state while enjoying a cloak of semi-protected ‘status’ for their extracurricular activities, provided they are directed against foreign targets.”
“Cybercriminals are recruited to Russia’s national cause through a mix of coercion, payments and appeals to patriotic sentiment,” reads a 2017 story from The Register on Cybereason’s analysis of the Russian cybercrime scene. “Russia’s use of private contractors also has other benefits in helping to decrease overall operational costs, mitigating the risk of detection and gaining technical expertise that they cannot recruit directly into the government. Combining a cyber-militia with official state-sponsored hacking teams has created the most technically advanced and bold cybercriminal community in the world.”

A banner that ran on top of the Verified cybercrime forum for many years.
It’s probably worth noting that also present on both DirectConnection and Mazafaka were the core members of a prolific gang of online bank robbers called the JabberZeus Crew, who used custom versions of the ZeuS Trojan to steal tens — if not hundreds — of millions of dollars from hacked small businesses across the United States. In 2011, most of that crew was rounded up in an international cybercrime crackdown, although virtually all of them escaped prosecution in their home countries (mainly Russia and Ukraine).
I mention this because K0pa also was in regular communications with — if not a core member of –the JabberZeus crew. This gang worked directly with the author of the ZeuS trojan — Evgeniy “Slavik” Bogachev — a Russian man with a $3 million bounty on his head from the FBI. The cybercriminal organization Bogchev allegedly ran was responsible for the theft of more than $100 million from banks and businesses worldwide that were infected with his ZeuS malware. That organization, dubbed the “Business Club,” had members spanning most of Russia’s 11 time zones.
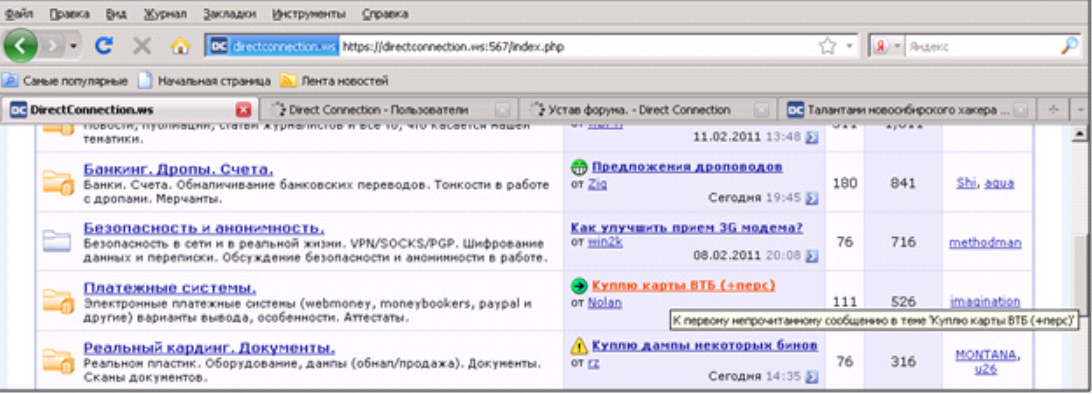
In this 2011 screenshot of DirectConnection, we can see the nickname “aqua,” one of the JabberZeus crime gang actors. K0pa also was affiliated with the JabberZeus crew.
Fox-IT, a Dutch security firm that infiltrated the Business Club’s back-end operations, found that beginning in late fall 2013 — about the time that conflict between Ukraine and Russia was just beginning to heat up — Slavik retooled his cyberheist botnet to serve as purely a spying machine, and began scouring infected systems in Ukraine for specific keywords in emails and documents that would likely only be found in classified documents.
Likewise, the keyword searches that Slavik used to scour bot-infected systems in Turkey suggested the botmaster was searching for specific files from the Turkish Ministry of Foreign Affairs – a specialized police unit. Fox-IT said it was clear that Slavik was looking to intercept communications about the conflict in Syria on Turkey’s southern border — one that Russia has supported by reportedly shipping arms into the region.
To my knowledge, no one has accused Burkov of being some kind of cybercrime fixer or virtual badguy Rolodex for the Russian government. On the other hand, from his onetime lofty perch atop some of the most exclusive Russian cybercrime forums, K0pa certainly would have fit that role nicely.
Further reading, including the fascinating story on the diplomatic back and forth between Russia and Israel mentioned in the first paragraph: The Russian Hacker Who Just Became One of Israel’s Most Famous Prisoners.
Premium Domain Names – transcom.uk
Transcom ISP – The UK’s Best Business ISP
DoubleCheck any website at doublecheck.uk